The SS7 network was once considered an environment that controls users’ access to network-based content and services, allowing licensed mobile operators to access customer data. However, many unlicensed entities currently have access to the SS7 network, taking advantage of the low security of this protocol. Consequently, more businesses and individuals with direct access to the […]


Many types of firewalls are often categorized by system protection, form factor, network placement, and data filtering method. Regarding 5G, Firewalls protect different network layers — especially in the Service-Based Architecture (SBA) of 5G Core. This includes: Perimeter Firewall (Traditional Role) It protects 5G infrastructure from external threats and is deployed at the edge of […]
Sunsetting 2G and 3G networks is not an easy step for mobile network operators (MNOs) due to several technical, financial, and social factors. The decision isn’t just about technology—it’s about customers, business strategy, and infrastructure readiness. One of the main challenges is the Legacy Device Support IoT and M2M devices: Many industrial machines, alarm systems, […]
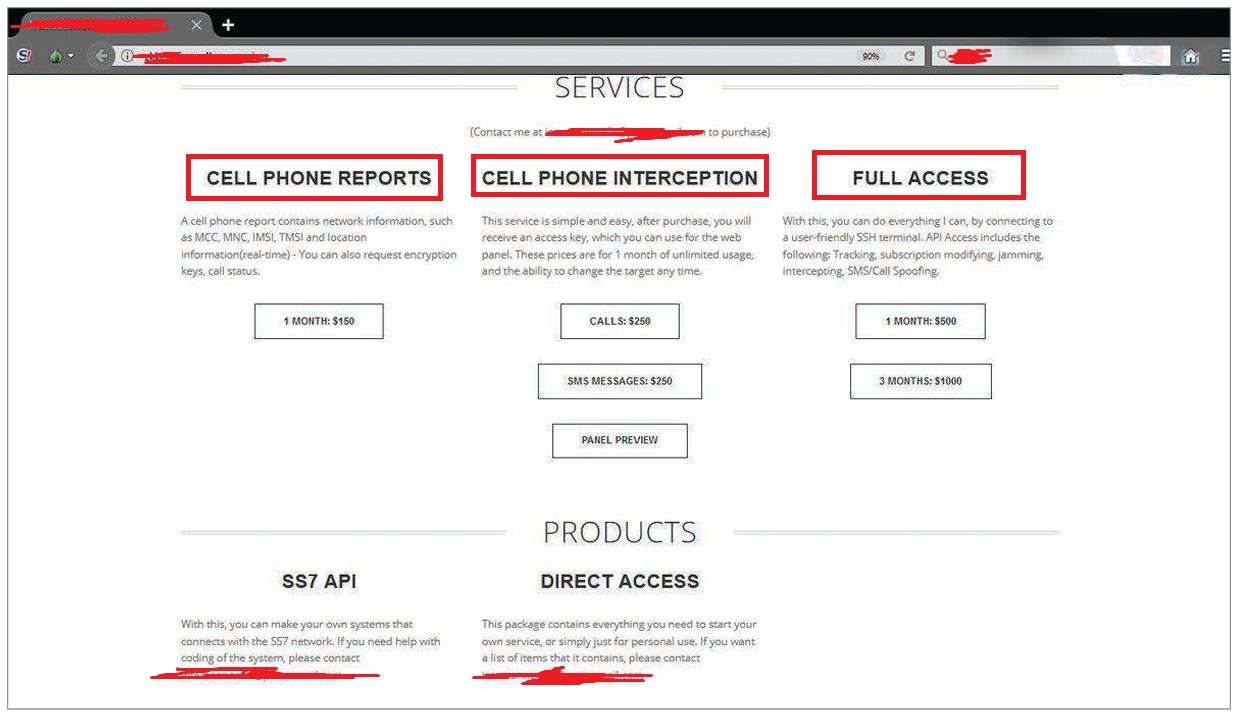
🔐 The SS7 network was once considered an environment that controls users’ access to network-based content and services, allowing licensed mobile operators to access customer data. However, many unlicensed entities currently have access to the SS7 network, taking advantage of its low security. Consequently, more businesses and individuals with direct access to the network, as […]
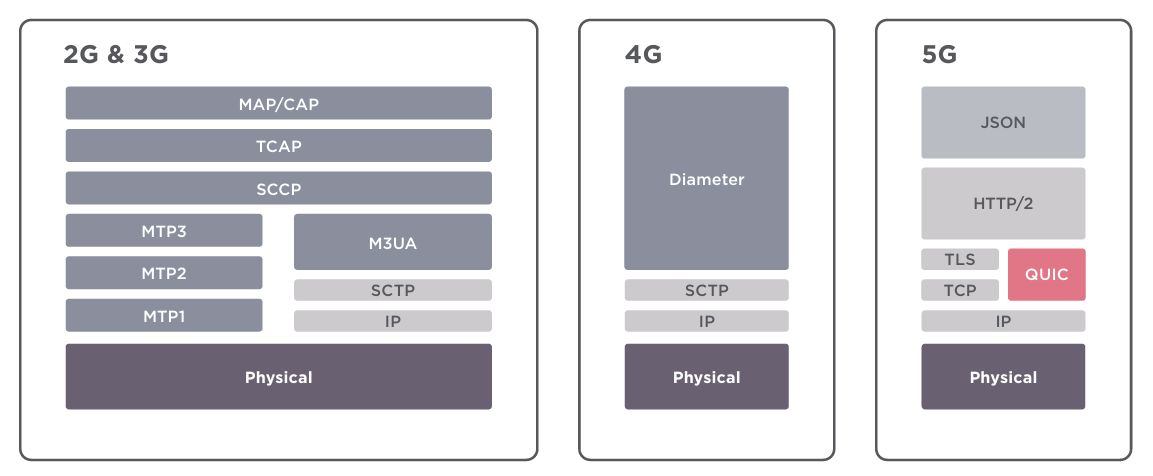
👉Previous generations relied on the SS7 and Diameter protocols. The 5G network core is built on well-known Internet protocols such as HTTP and TLS. 👉 Security threats associated with 3G and 4G will remain after 5G reaches the public and heavily influence NR deployments. However, the main challenge with 5G is that Internet technologies are […]

📃5Ghoul is the name given to a set of 14 newly discovered vulnerabilities in Qualcomm and MediaTek 5G modems, disclosed in December 2023 by researchers from the Singapore University of Technology and Design (SUTD). These vulnerabilities affect hundreds of smartphone models and allow cyberattacks on 5G-enabled devices. 👉5GHoul = 5G + Ghoul, an Arabic mythology. […]
👉 The first 2G mobile network in the world was launched in Finland in 1991, marking the first digital mobile network and replacing analogue 1G systems. 👉 The Nokia 1100, launched in 2003, remains the best-selling phone of all time, with over 250 million units sold. Also, it had a firmware bug that hackers could […]
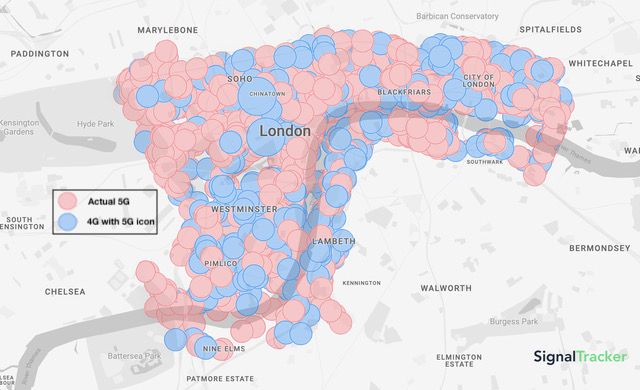
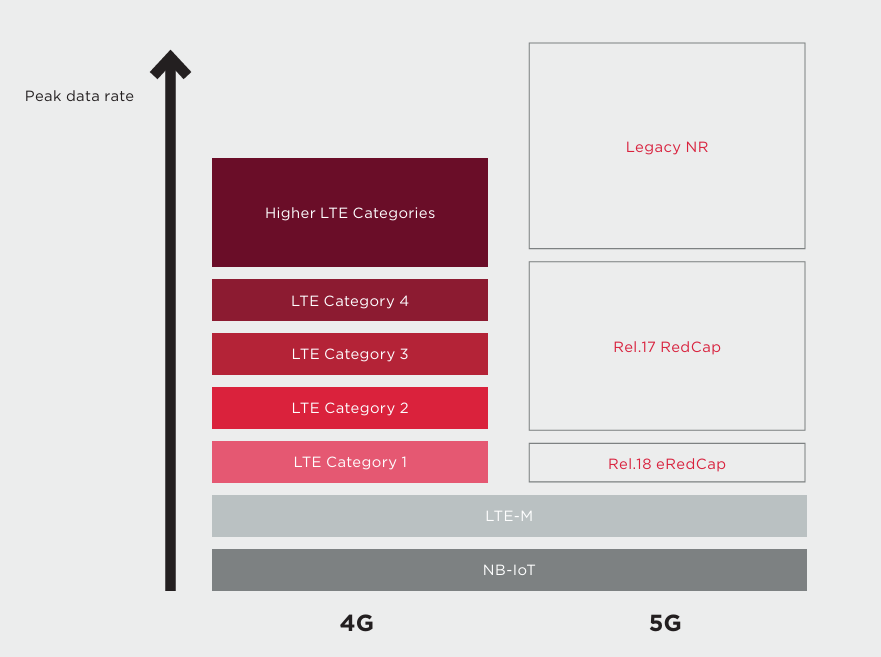
The Question is Actual 5G or Icon-only 5G! Recently, a new mobile app called SignalTracker showed that nearly 40% of 5G connections are actually 4G, as per PolicyTracker. Actual 5G is about twice as fast as icon-only connections, averaging 49 Mbps compared to 27 Mbps in our tests. In UK tests, when the 5G icon […]
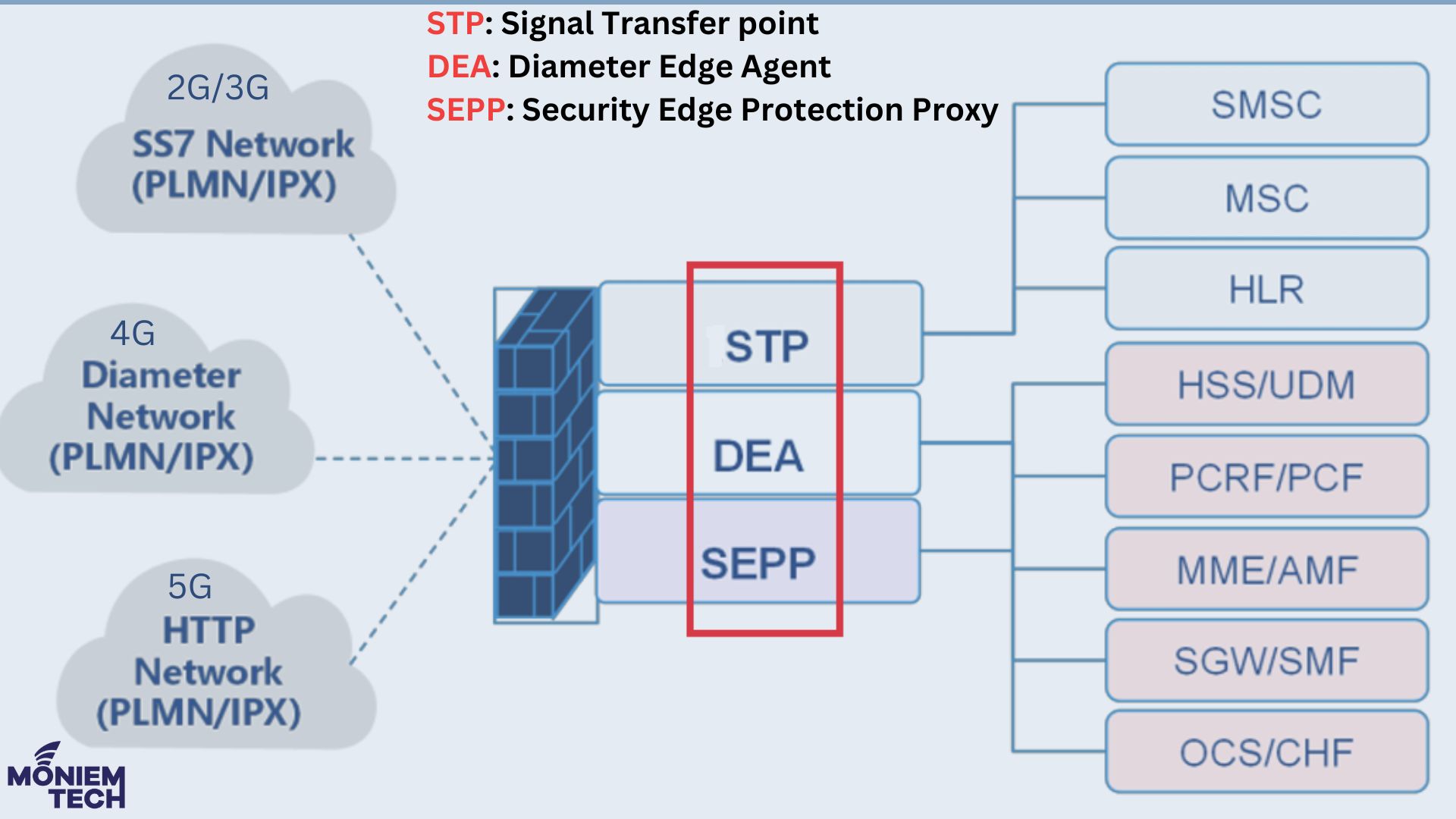
The journey started with 2G and 3G, where Voice was the leading service, and the main protocols were SS7 and SIGTRAN (Signaling Transport). At this time, the primary Firewalls are: SS7/SIGTRAN Firewall: Its functions are national/international interconnect protection with different policies and detection patterns in real-time. GTP Firewall: The functions are GTP Packet binary checks […]
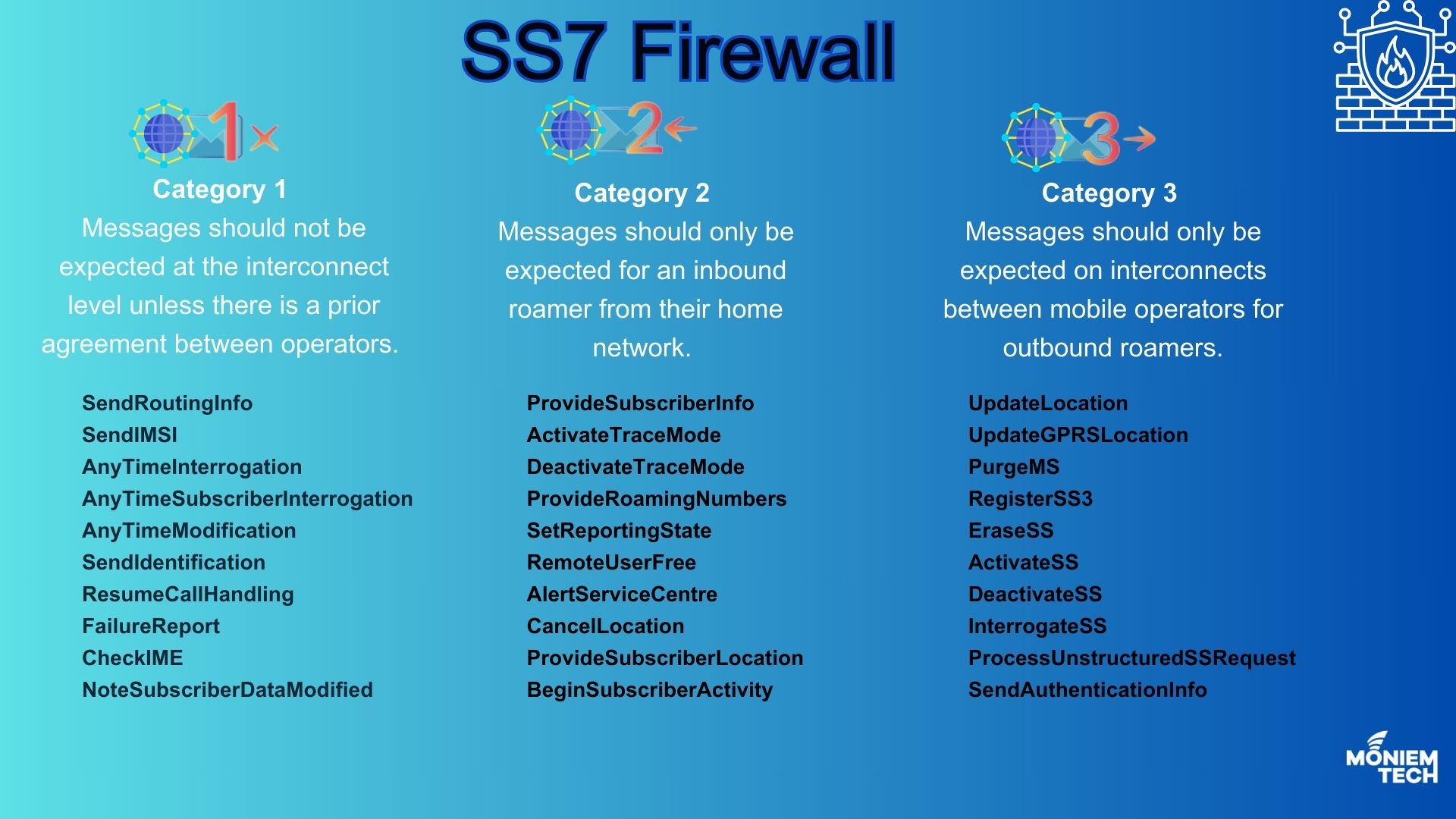
SS7 was never designed with security in mind, so it has always been open to internal and external threats. S7 Firewall is a smart, rules-based system that can monitor, create rules, and enforce policies to prevent or mitigate the effects of these attacks. It is essential for safeguarding your network and subscribers. The GSMA’s FS.11 […]
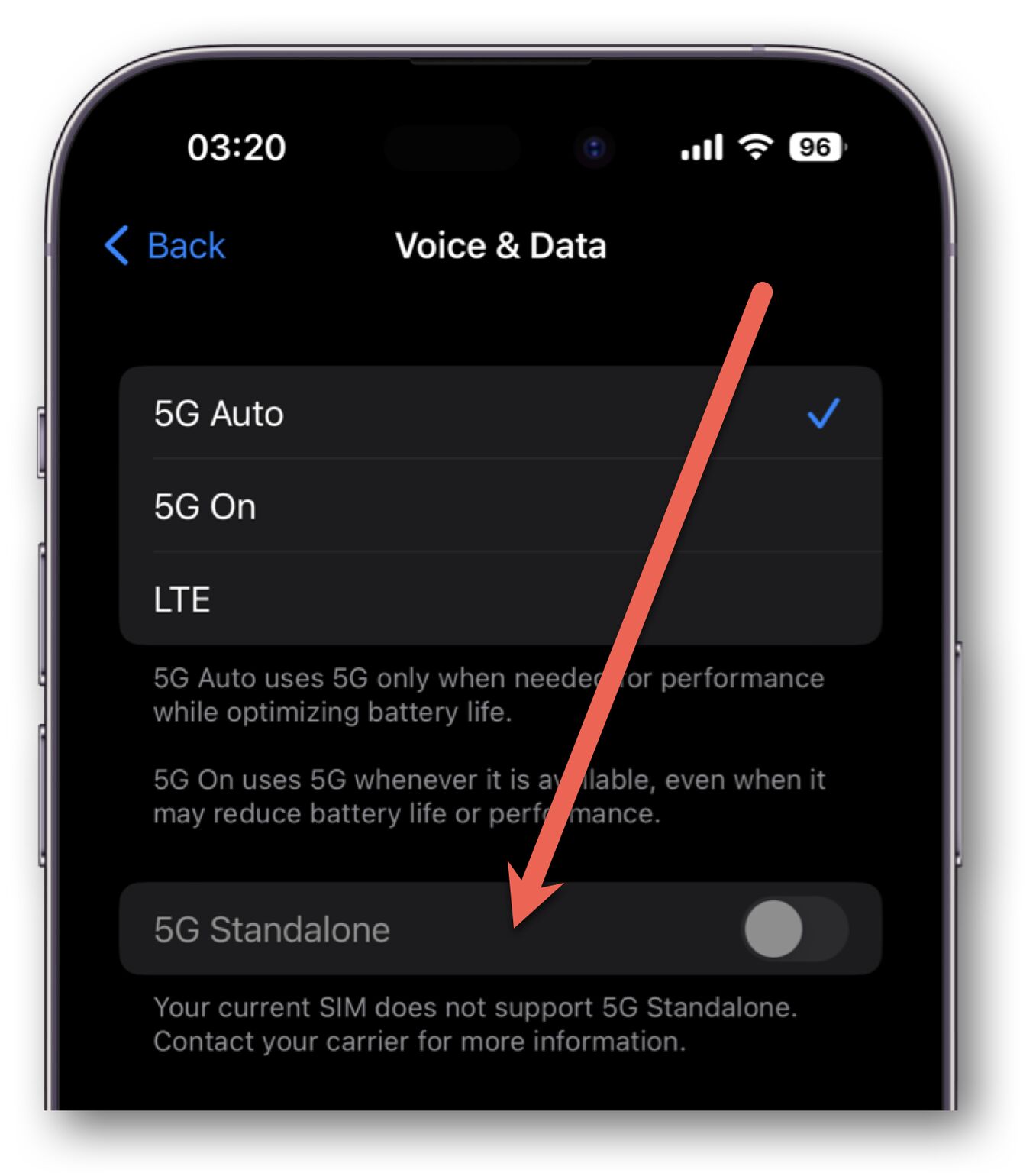
When I started my 5G Journey in 2017, I first explored the 5G network versions: 5G NSA (Non-Standalone) and 5G SA (Standalone). Most MNOs envision starting with 5G NSA and moving towards the full capabilities of 5G SA. However, the reality of 5G SA has so far proved somewhat different from the vision. Here, I […]
