Imagine being able to download every HD video on Netflix in just one second… Now, with Japan, we can say yes. Japan’s National Institute of Information and Communications Technology (NICT) achieved […]

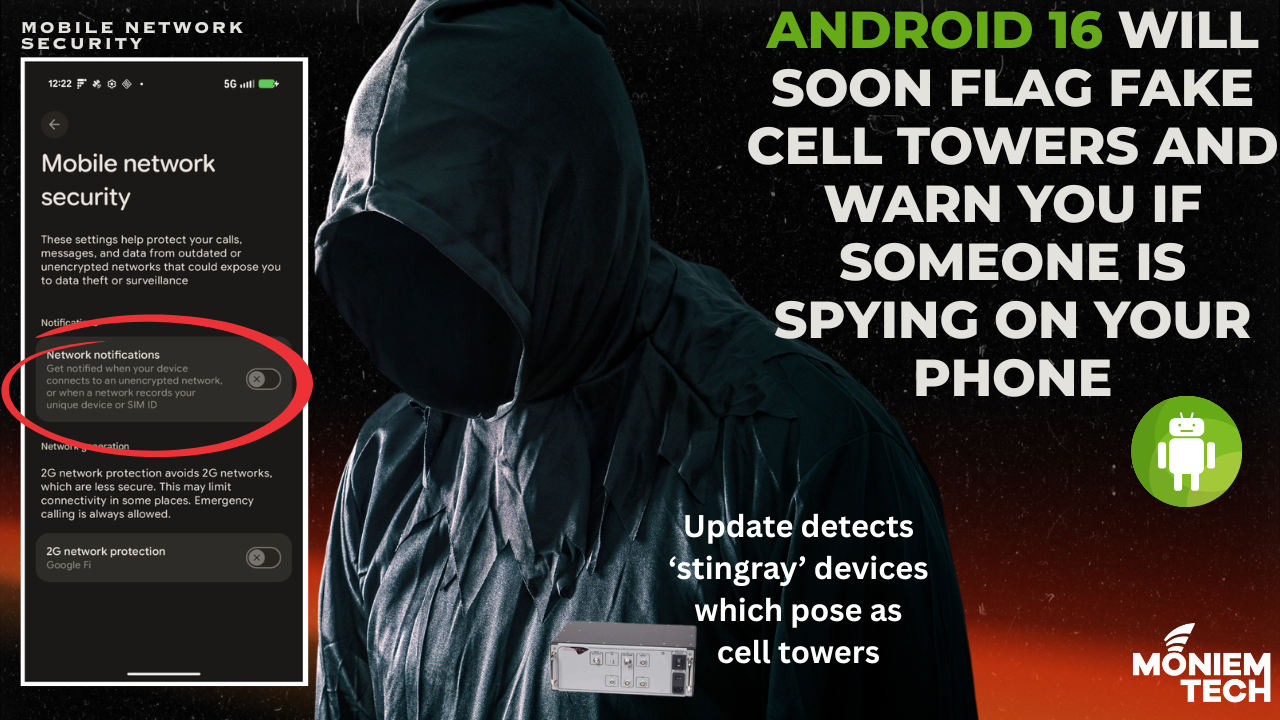
The upcoming Android 16 release introduces a critical new security feature: Network Notification Warnings This enhancement is designed to alert users in real time when their mobile devices are exposed […]
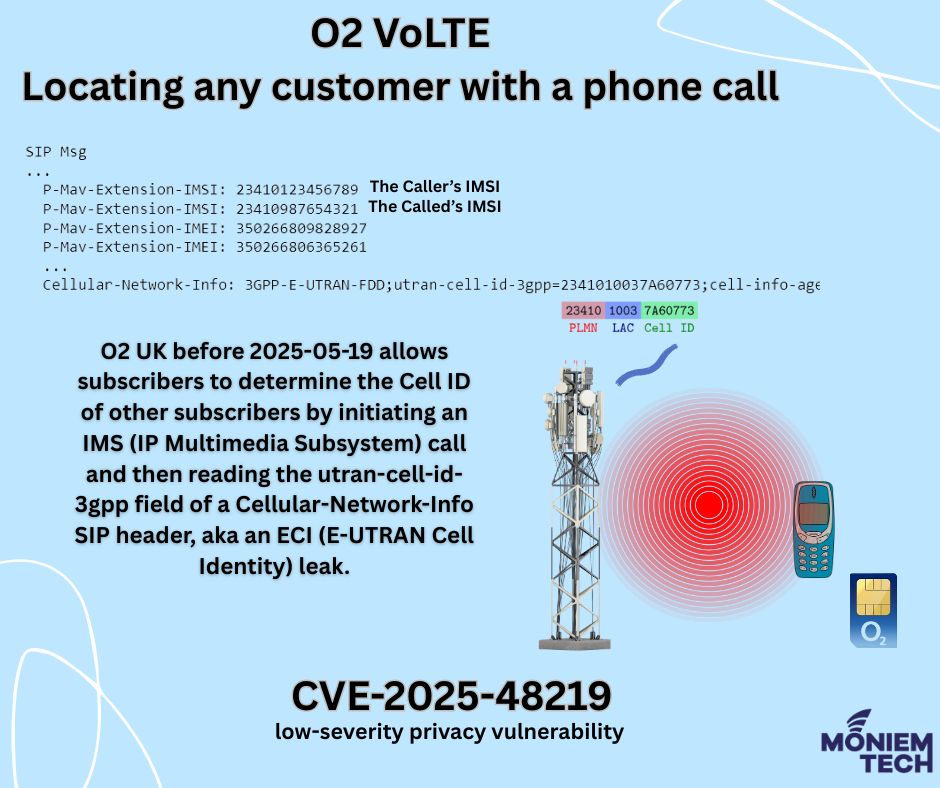
Vulnerability Details: CVE-2024-53026. It is a vulnerability affecting O2 UK’s VoLTE/IMS service, disclosed in mid-May 2025. Rated Low, with a CVSS v3 score of 3.5. It has a limited impact on confidentiality […]
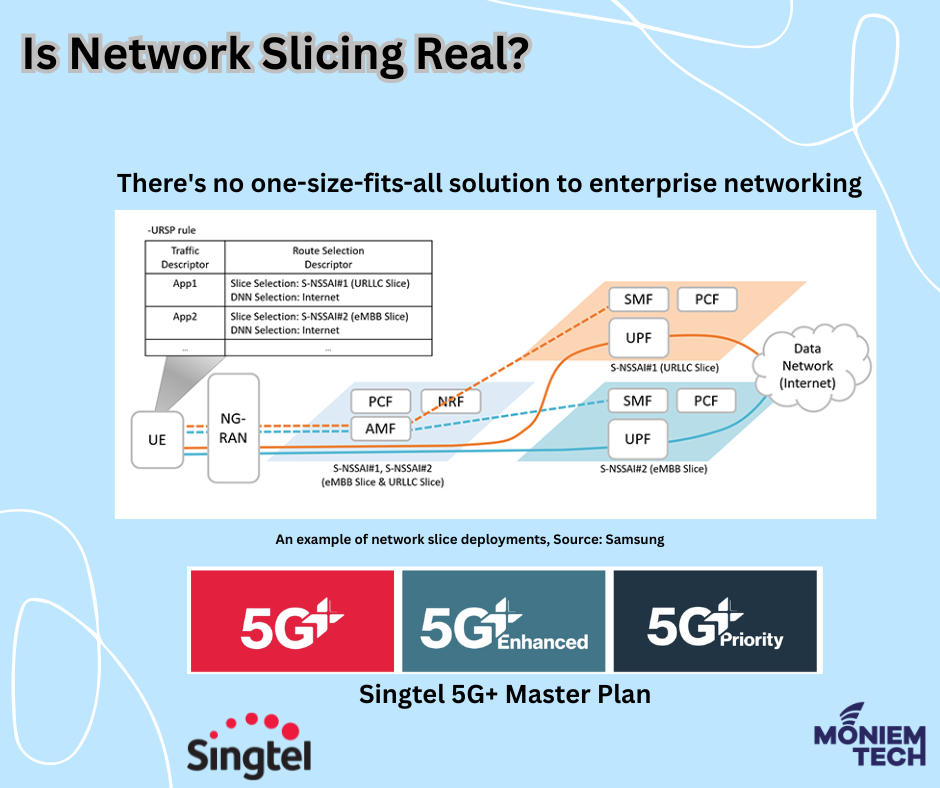
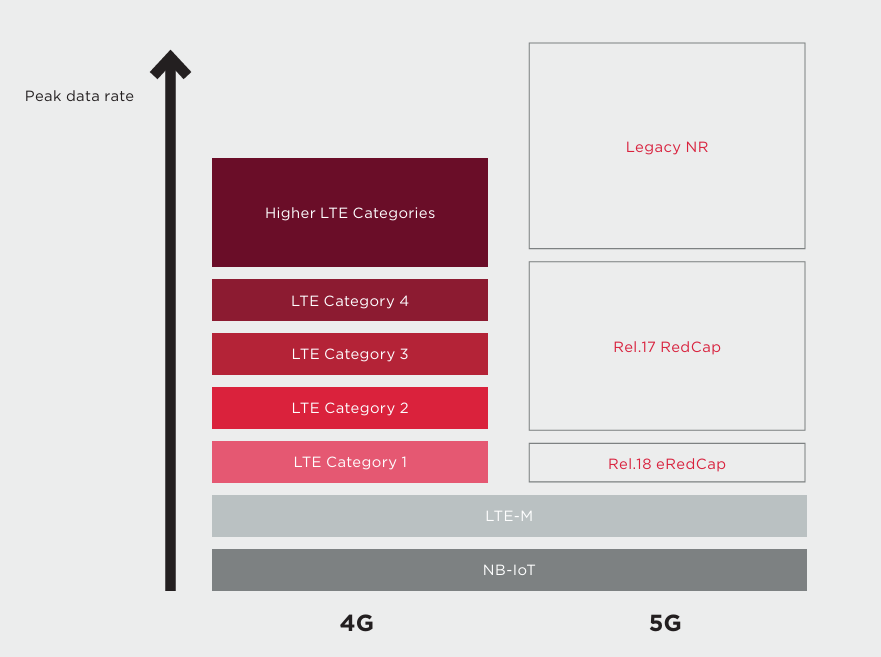
Network Slicing is essentially the ability to divide your network into individual use cases, each tailored to provide specialised services. Traditionally, in 4G, the APN (Access Point Name) was probably […]
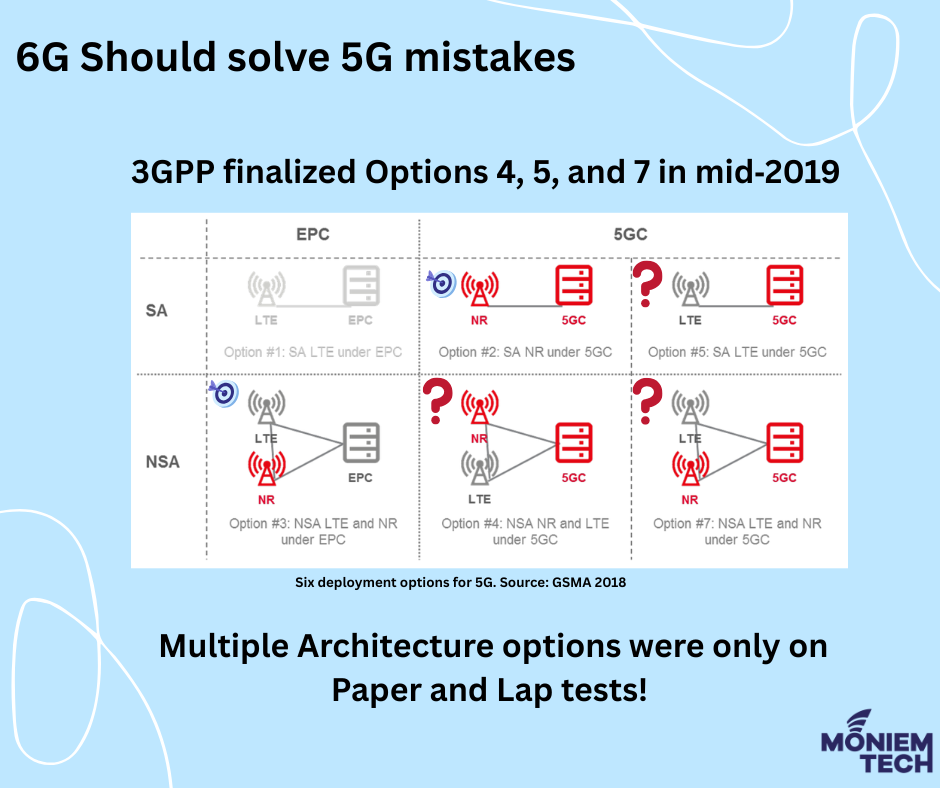
For the introduction of 5G, 3GPP has specified five possible configurations, or ‘options’, for connecting to an EPC or a new 5G core network (six if the current 4G system […]

Synchronization in 5G ensures precise timing and coordination across the network, enabling key technologies like TDD, beamforming, and ultra-low latency. 5G TDD networks utilise the same frequency for both uplink […]
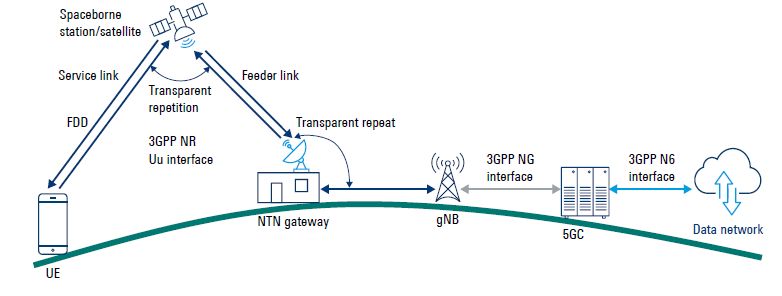
The 5G Non-Terrestrial Network (NTN) integrates satellite and airborne platforms with terrestrial 5G networks to provide ubiquitous coverage. The Next-Generation Radio Access Network (NG-RAN) architecture in 5G NTN can be designed to […]
Interworking security between 5G and EPC involves managing security contexts during mobility between the two systems. This ensures that the UE can maintain secure connections regardless of the access […]
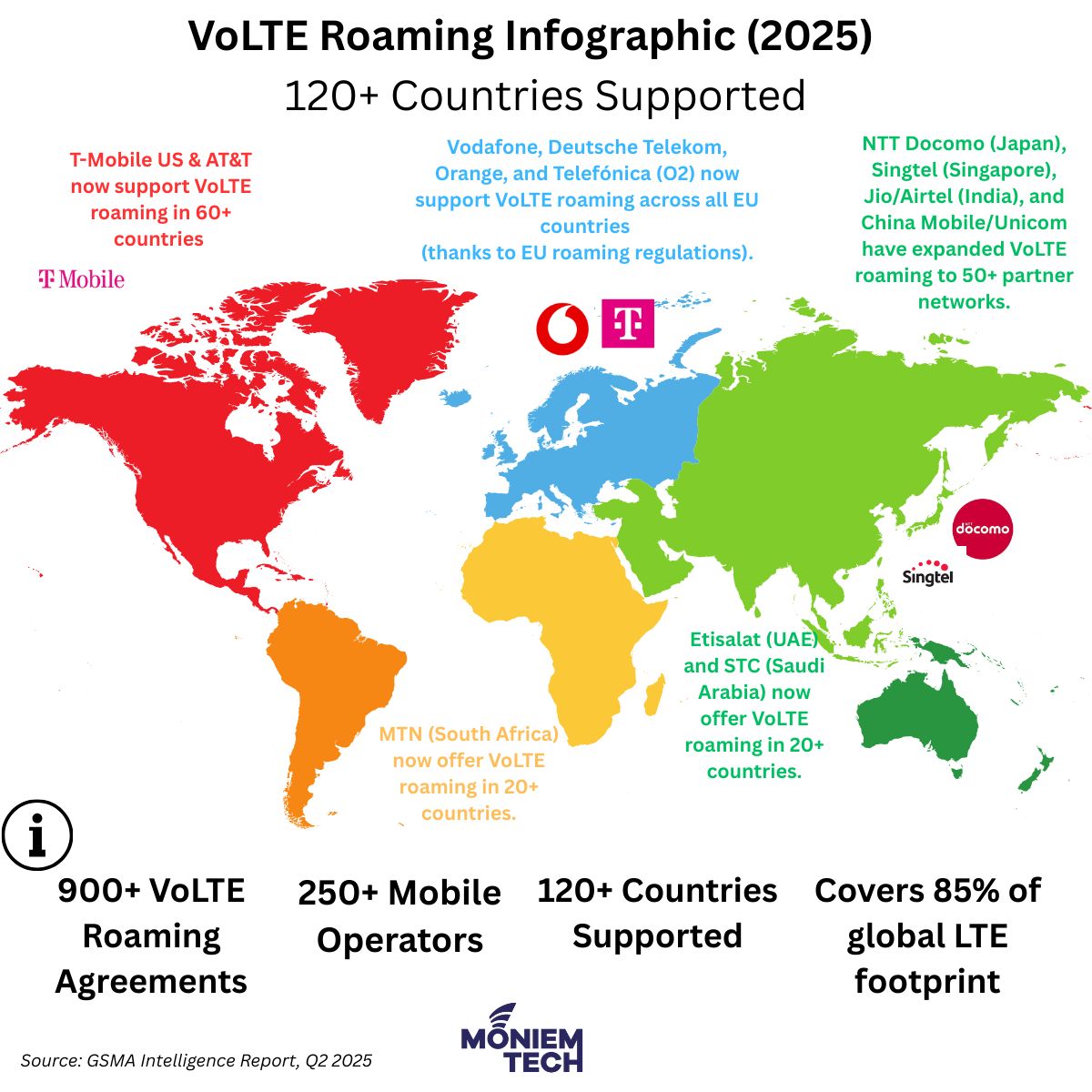
As of April 2025, the global landscape of Voice over LTE (VoLTE) roaming agreements has expanded significantly, reflecting the industry’s shift towards all-IP voice services and decommissioning legacy 2G/3G networks. […]

The blackout, which began around midday, disrupted essential infrastructure, including mobile networks, internet services, and emergency communication systems. In both Spain and Portugal, users experienced difficulties with voice calls, and […]
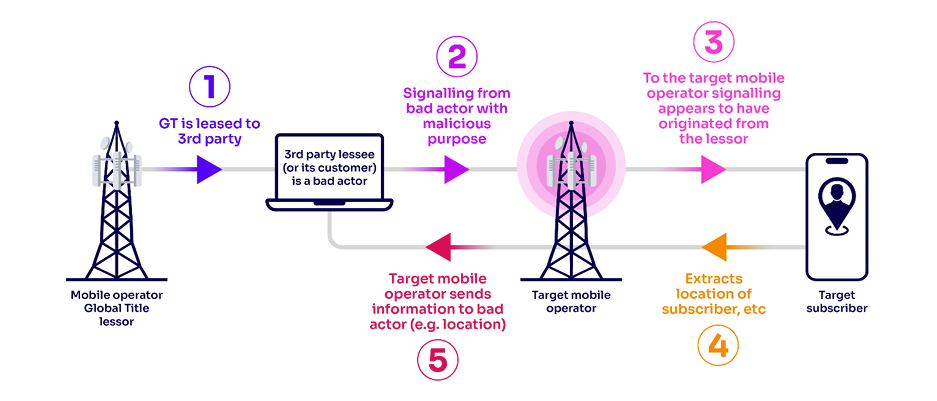
I wrote an article before about ” What is GT (Global Title)? Why Do We Need It?” What is Global Title Leasing? GT leasing is the practice of a mobile […]
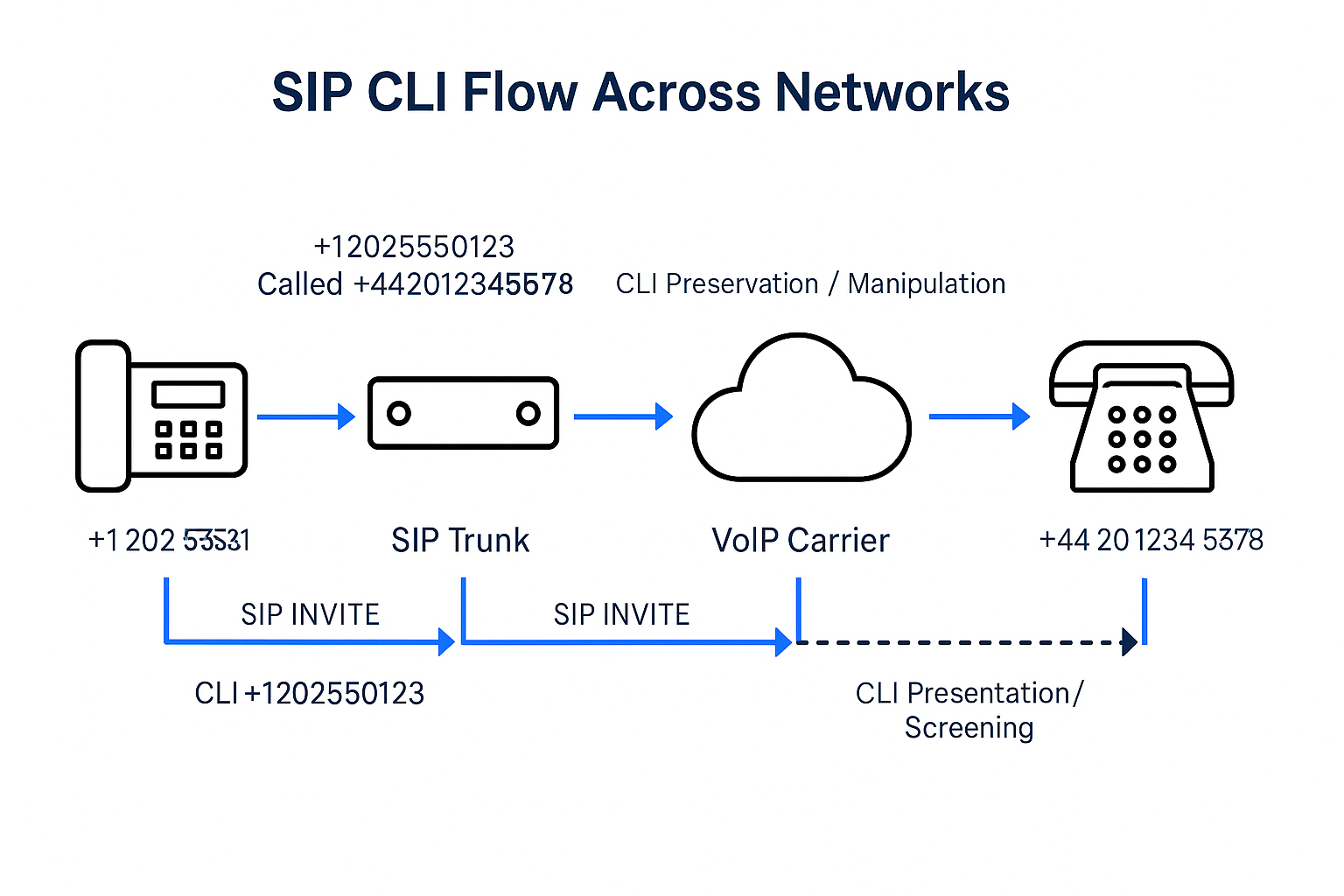
Last weekend, by coincidence, I found a fraud story related to the Telecom domain called “Spoofing CLI” or “Calling Line Identification (CLI) spoofing.” which is a technique used in mobile […]
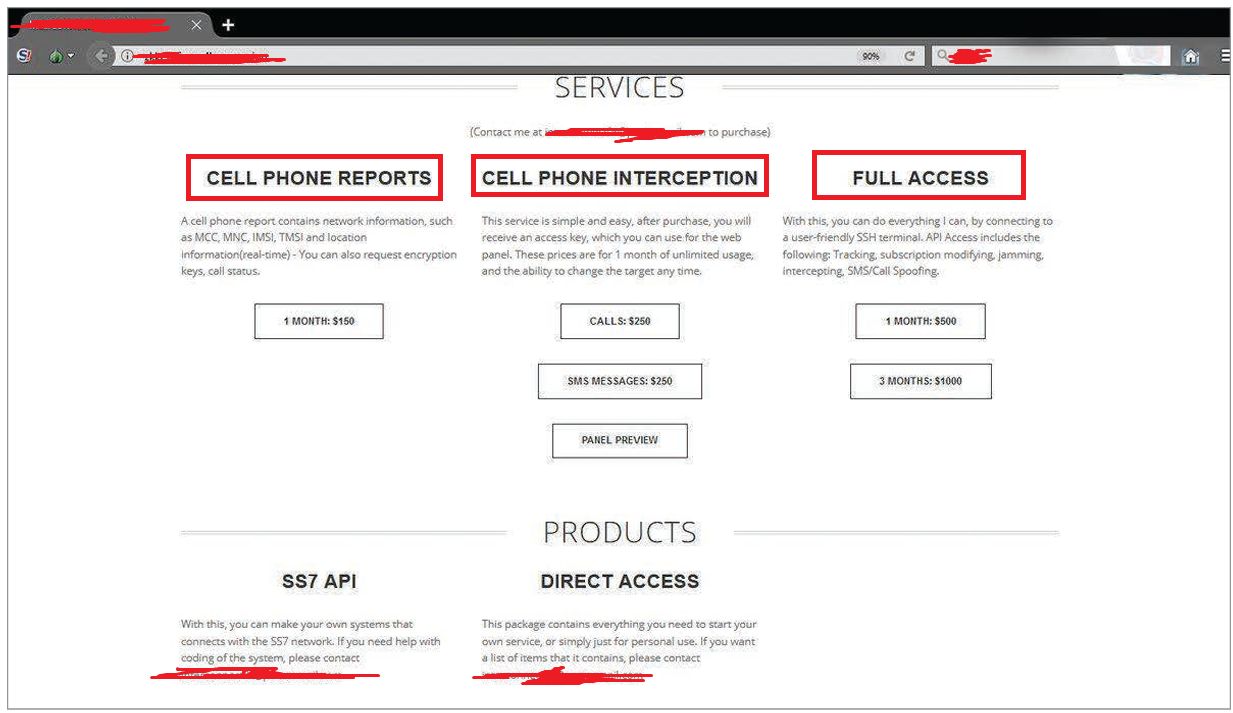
The SS7 network was once considered an environment that controls users’ access to network-based content and services, allowing licensed mobile operators to access customer data. However, many unlicensed entities currently […]

Many types of firewalls are often categorized by system protection, form factor, network placement, and data filtering method. Regarding 5G, Firewalls protect different network layers — especially in the Service-Based […]
Sunsetting 2G and 3G networks is not an easy step for mobile network operators (MNOs) due to several technical, financial, and social factors. The decision isn’t just about technology—it’s about […]
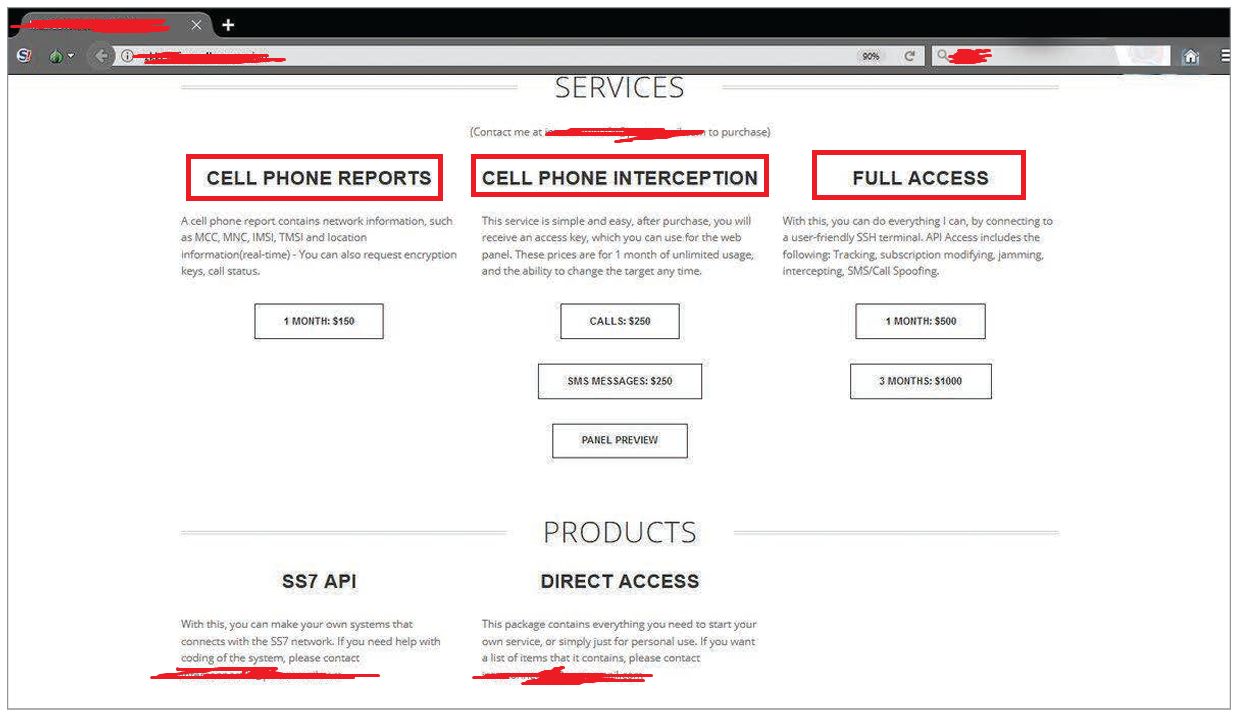
? The SS7 network was once considered an environment that controls users’ access to network-based content and services, allowing licensed mobile operators to access customer data. However, many unlicensed entities […]
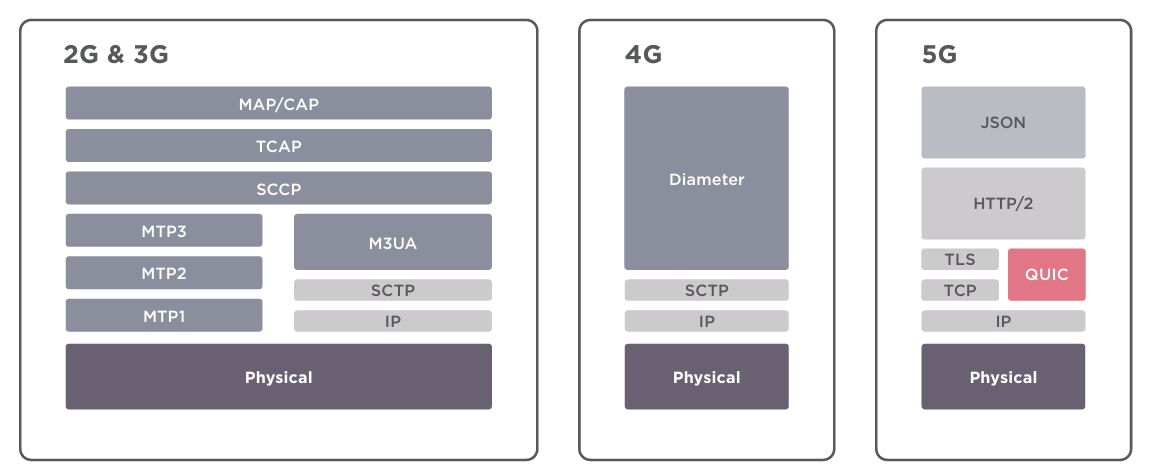
?Previous generations relied on the SS7 and Diameter protocols. The 5G network core is built on well-known Internet protocols such as HTTP and TLS. ? Security threats associated with 3G […]

?5Ghoul is the name given to a set of 14 newly discovered vulnerabilities in Qualcomm and MediaTek 5G modems, disclosed in December 2023 by researchers from the Singapore University of […]

? The first 2G mobile network in the world was launched in Finland in 1991, marking the first digital mobile network and replacing analogue 1G systems. ? The Nokia 1100, […]

The Question is Actual 5G or Icon-only 5G! Recently, a new mobile app called SignalTracker showed that nearly 40% of 5G connections are actually 4G, as per PolicyTracker. Actual 5G […]
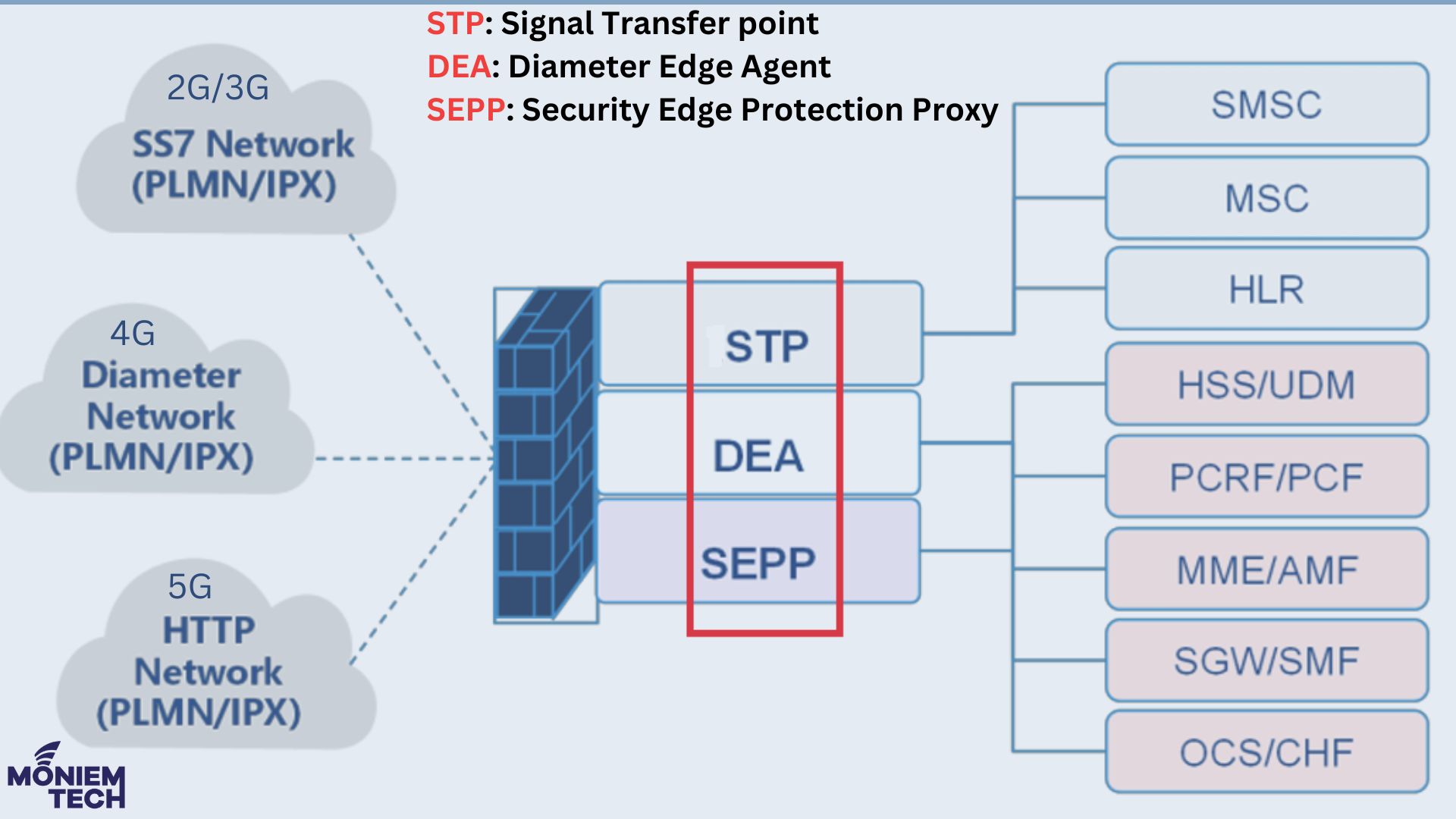
The journey started with 2G and 3G, where Voice was the leading service, and the main protocols were SS7 and SIGTRAN (Signaling Transport). At this time, the primary Firewalls are: […]
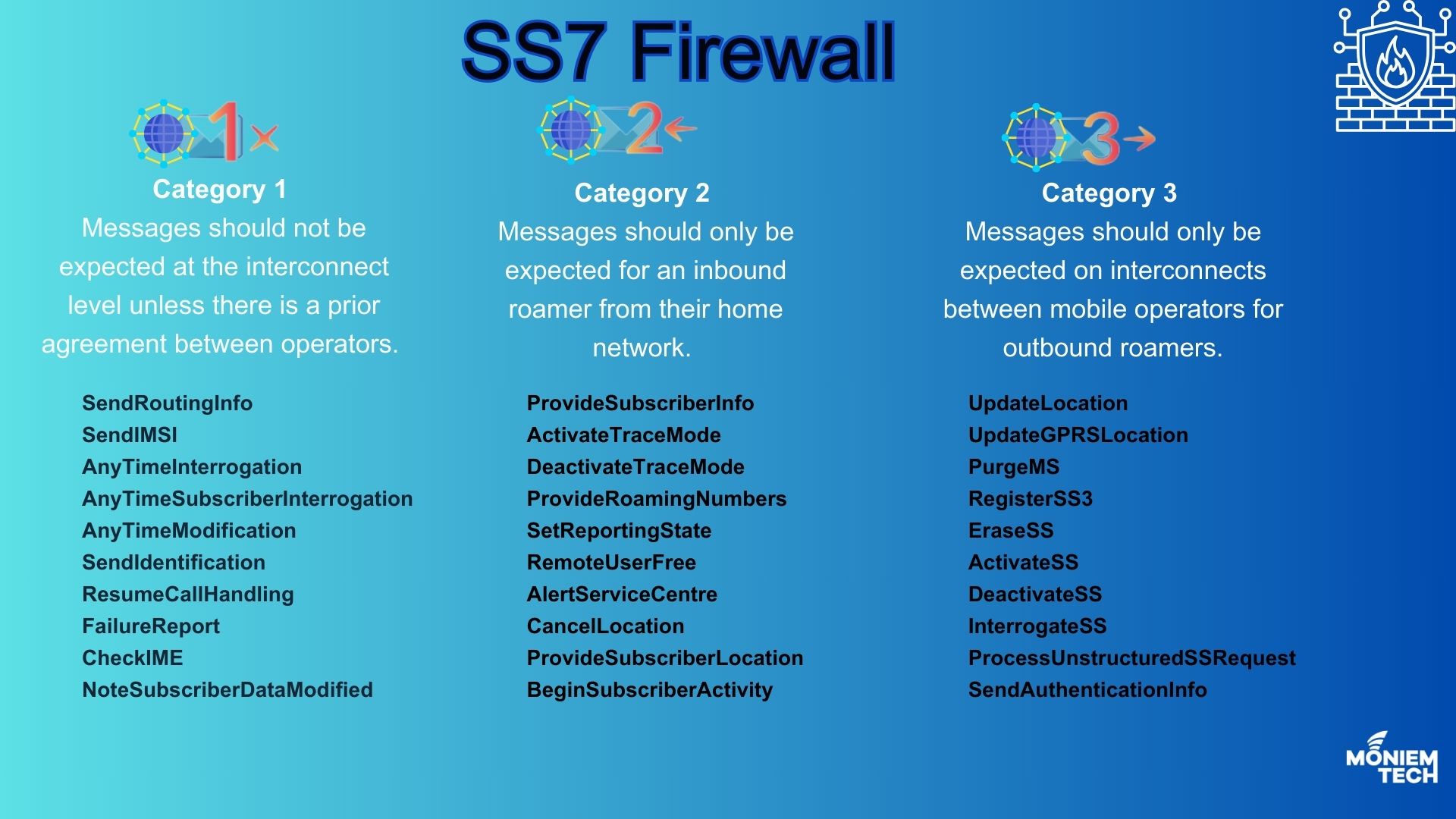
SS7 was never designed with security in mind, so it has always been open to internal and external threats. S7 Firewall is a smart, rules-based system that can monitor, create […]

When I started my 5G Journey in 2017, I first explored the 5G network versions: 5G NSA (Non-Standalone) and 5G SA (Standalone). Most MNOs envision starting with 5G NSA and […]
Voice calls remain one of the most vital means of communication in both personal and professional spheres. They provide instant and direct interaction, allowing for clear and immediate conversations. Unlike […]
